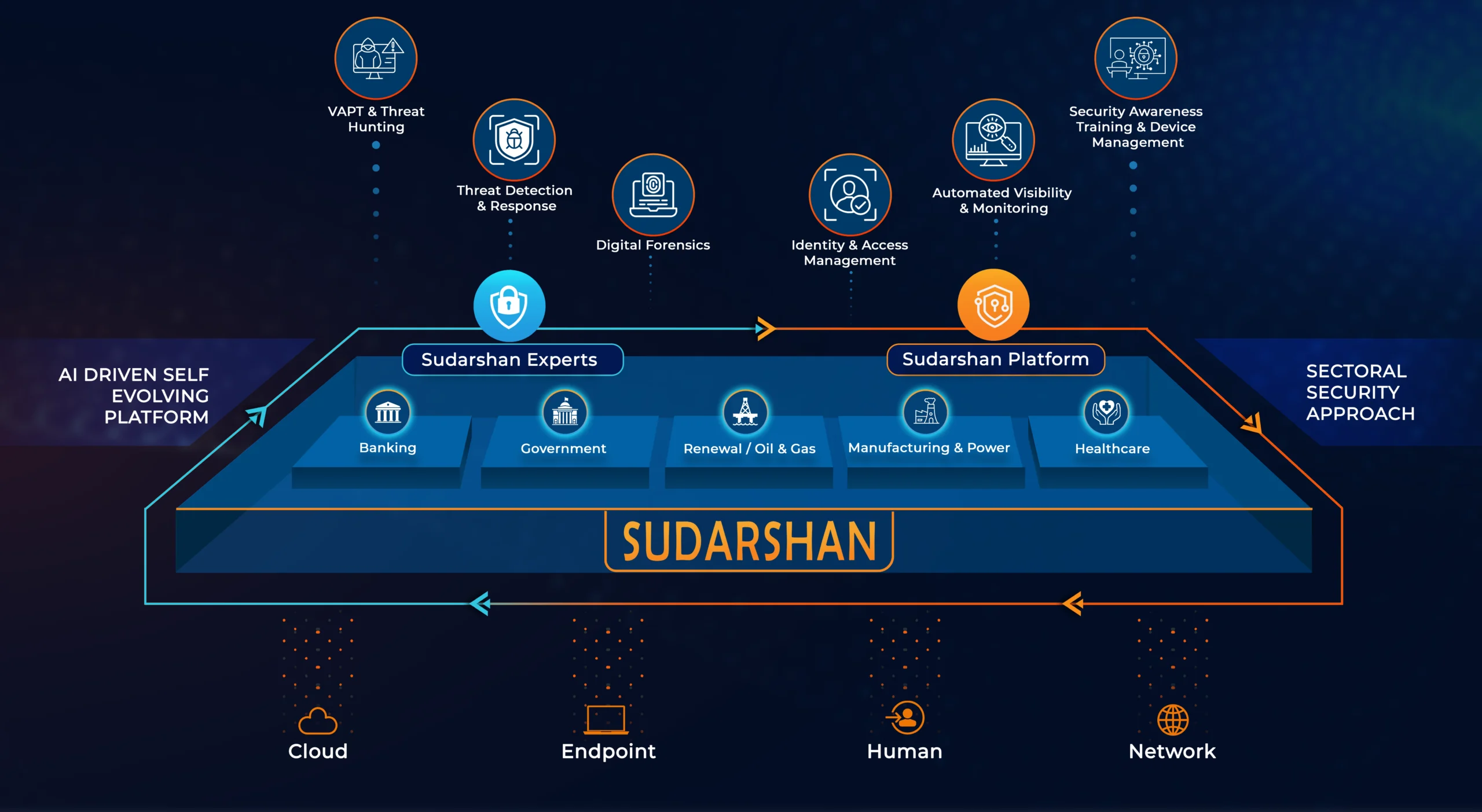
Automated Cyber Intelligence Managed Platform
Sudarshan MSSP
Sudarshan is a multi-tier, multi-tenant platform that combines the power of a hybrid Security Operations Center with the unparallel advantage of an Advanced SIEM and EDR Sudarshan offers defense in-depth cyber security, managed and monitored by the MSSP. With all the essential tools, analytics, dashboards, controls, queries and reports at your fingertips, it enables an elevated security posture for customers across any sector, ensuring that all their digital assets – whether in the cloud, on-premise or remote workplace are monitored and protected effectively 24×7.

Sudarshan Security Labs
Sudarshan Security labs delivers proprietary technology providing unparalleled threat detection and response for our customers and security community at large.
Features
Rapid MSSP Onboarding
Achieve MSSP onboarding in just 1 hour with hassle-free entitlements managed through intuitive user and role configurations.
Tenant-based Data Segregation
Ensure security and organization with the separation of data, configurations, rules, reports, and assets by tenant, providing a structured and tailored environment.
Comprehensive Tiled Dashboard
Access a tiled dashboard presenting summary Key Performance Indicators (KPIs), security alerts, and system alerts for a quick, comprehensive overview.
Forensic Search Capabilities
Conduct forensic searches on raw logs based on specific time periods and individual tenants, enabling precise and insightful analysis.
Efficient Pre-built Templates
Utilize pre-built templates for seamless setup of log archives, notifications, and SSL configurations, ensuring efficiency and consistency in your operations
Enhanced Threat Intelligence Integration
Strengthen your defenses with additional threat intelligence, easily imported via file-based methods or ingested through the STIX-TAXII interface for up-to-date security measures.
Services
Manage
- Incident & Alerts
- Threat Hunting
- Policy Violations
- Provisioning
- System Health
- Reporting
- Notifications
Extended Detection
- Behavioral Anomalies (ML)
- Advanced Correlation (AI)
- Dynamic Threat Models
- Endpoint Threat Detection
- Network Based Detection
- Vulnerability Assessment
Rapid Remediations
- Automated Response *
- Alert Based Recommendation
- Semi - automated Response *
- Endpoint Quarantine
- Network Based Isolation
Get in touch for a complimentary cyber security consultation.
Frequently Asked Question's
The provision of security devices and system surveillance and control through outsourcing is the function of a managed security service provider (MSSP). Common services include managed firewall, intrusion detection, virtual private network, vulnerability assessment, and anti-viral services. MSSPs offer 24/7 services through high-availability security operation centres (hospitable centres they own or those of other data centre providers). These services are designed to decrease the quantity of operational security personnel that an organization must recruit, educate, and retain to sustain a satisfactory security stance.
Both MSPs and MSSPs provide third-party services to organizations, but their purposes differ. The MSSP handles security, whereas the MSP handles network, application, database, and other IT support. When something goes wrong, an MSP is called. A network operations centre (NOC) helps MSPs monitor events and reports and reduce downtime. A high-availability security operations centre (SOC) protects customer data and systems for MSSPs. MSPs often cooperate with MSSPs that offer controlled detection and response, breach detection and prevention, incident planning and management, and more.
- Monitoring and identifying intrusions on IT infrastructure is the area of expertise of MSSPs, which they employ to protect businesses from online threats.
- They effectively balance affordability and high security by collaborating with security specialists and employing standardized templates.
- Q leverage in the banking industry demonstrates that managed security services can safeguard IT systems without requiring substantial initial investments.
- Enterprises are safeguarded around the clock without the need for external contractors. Instead, they rely on their internal personnel and cutting-edge technology to defend against cyberattacks rapidly and effectively.
- Data protection and a diminished likelihood of data loss are accomplished through the prompt and reliable security services provided by MSSPs.
MSSPs provide a wide range of cybersecurity services to protect enterprises against evolving cyber threats. These services typically include:
- Security monitoring and management include monitoring cloud environments, endpoints, and network traffic for suspicious activity.
- To reduce the attack surface, vulnerability management detects, evaluates, and fixes system and application vulnerabilities.
- For Threat detection and prevention, execute security solutions to prevent malware infections, breaches, and other intrusions.
- Incident response includes rapid containment, elimination, and recovery of security incidents. Support compliance with data privacy and industry rules.
- Security awareness training teaches employees the best cybersecurity practices to reduce human error.
MSSP helps and assists your business to stay protected and secured in the same way that a security officer might serve. Being in alert mode and staying prepared in advance, they will keep an eye on your network and immediately take mandatory actions to protect it from risks. In some ways, it is similar to how an internal security team works to how a SOC works. It's not a contractor, even though they protect your business from hacking.
SIEM, or “Security Information and Event Management” is a program that helps organizations to investigate, detect and eliminate security threats before they disrupt operations. SIEM, pronounced "sim," is a security management system that combines security event management (SEM) and security information management (SIM). SIEM system collects event log data from several sources, employs real-time analysis to detect abnormal behaviour, and then takes appropriate action. SIEM lets businesses monitor what's going on in their network so they can respond swiftly to any attacks and meet regulatory obligations.
SIEM is the software utilized by security professionals that provides a real-time, comprehensive view of the cybersecurity posture of an organization. It functions by gathering, overseeing, and subsequently identifying associations between log and event data. It is capable of identifying hazards and notifying analysts in a timely manner, enabling them to take appropriate action. It is also incorporated into the SOC software. Managed SOC utilizes a staff of engineers and analysts and SIEM technology to identify, assess, and respond to cybersecurity threats, in addition to maintaining a constant vigilance against cyberattacks.
XDR provides a unified view of all security data across all devices, networks, the cloud, and SaaS applications for an entire organization. The integration of data from multiple sources facilitates the detection and mitigation of threats. MDR is a service that employs external malware specialists. Constantly monitoring a company's network and connections for threats and preventing them from causing harm, MDR teams keep an eye out for them. The SIEM collects, analyzes, and stores security data from various company departments. Security data that identifies trends and patterns can be utilized to generate reports and alerts.
SIEM relies on event archives and practical security intelligence. A single platform provides security intelligence from all sources. EDR searches for and responds to ransomware, file-less assaults, and malware at the endpoint. EDR only collects endpoint data. SIEM gathers data from endpoints and other sources. The multi-layered log-gathering method includes on-premises, cloud, network, user, and application architecture. Seeking danger Log analysis is limited by source data. SIEM uses machine learning to analyze large records. SIEM's conclusions may be similar to EDR's because EDR just records endpoint data.
For the protection of laptops, workstations, and servers, EDR is implemented. Using endpoint data, threats are identified, and responses are generated. XDR incorporates endpoint, network, cloud, and SaaS data for security purposes. Correlating data from multiple sources, XDR is capable of identifying hazards that EDR failed to detect. EDR is less advanced than XDR. Its deployment is more complex and expensive. Organizations searching for endpoint protection at a reasonable cost should consider EDR. Organizations in search of a more comprehensive solution to safeguard against a greater number of hazards should consider XDR.
Signature-based monitoring for Endpoint Protection Platform (EPP) proactive threat prevention slows IOC response. It only partially explains endpoints. Endpoint Detection and Reaction (EDR) investigates and remedies security breaches. EDR employs anomaly identification and machine learning to discover new threats more precisely. Endpoint event data from EDR's active monitoring provides a complete picture of activities and allows real-time replies. It offers EDR more authority to investigate and respond to security occurrences than EPP's restricted but preventive approach.

